How to secure your private keys? Why are offline storage devices considered safe?
May 19, 2021 22:15
Stepping into 2021, cryptocurrencies have become the hottest topic among all in the financial world. However, not all people are able to grasp knowledge about cryptocurrencies and about their security.
Cryptocurrencies are specially designed currencies to provide the power of finance in the hands of their users, but at the same time, these are liable to cyberattacks. You can visit bitcoin trading to learn more about bitcoin trading. The most important thing that one must keep in their mind is about storing private and public keys safely to make safe transfers and to secure bitcoins from cybercrimes. Every crypto holder must learn ways, methods, or tips to keep private keys safe.
Digital keys: Public and private keys
If you have gained knowledge about cryptocurrencies, then as of now, you must know that cryptocurrencies term is an amalgamation of cryptography and currencies. Cryptography is a method to encode and decode information to keep the data safe. Blockchain is the technology on which the entire bitcoin network is built, and cryptography is an important feature of blockchain technology. Cryptography in blockchain technology is responsible for making it decentralized means removing the involvement and interference of any third parties that can be government or financial institutions.
The blockchain is required to confirm all the bitcoin transactions and to verify and validate the transactions; blockchain uses an encrypted mathematical puzzle that matches both public and private keys. Public and private keys are a long string of numbers that provide ownership of digital wallets. A digital wallet must be created to store the crypto coins, and when a crypto holder creates a new wallet, the public and private keys are generated. A public key is used to encrypt the data or code, whereas private keys are used to decrypt the data.
Private Key is of high importance as it is used to send and receive crypto tokens and to make purchases. For making transactions and purchases, you need to provide your public Key to another party. Each transaction needs to be signed digitally through private keys, which means that private keys act as a digital signature for your transactions. Private keys are used to prove ownership of coins, and a new public key can be generated using private keys.
Ways to keep your private keys secured
One of the popular ways to secure your private keys is by using a paper wallet that generates and prints private keys on a piece of paper. Paper wallets are a type of cold storage wallets that not able to be forfeited and are immutable to cybercrimes. But if a paper wallet is lost, you can never recover it. You can store your private keys that are printed on paper in a safe vault or safe deposit box.
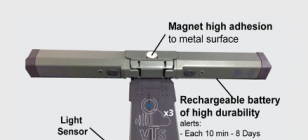
Another best way to store your private keys securely is by storing them in offline wallets. The best offline wallet is a hardware wallet that stores private keys in the offline storage device. Offline wallets are secure wallets that aim at providing high security to cryptocurrencies by storing them offline. The offline wallets are never connected to the internet and allow users to make transactions wirelessly.
You can also choose to store your private keys on your mobile device or computer means in mobile wallets or desktop wallets. These are highly convenient wallets that enable users to access and transfer funds easily. These types of wallets are hot wallets that require an internet connection, and also, these are susceptible to viruses, hackers, malware attacks, and phishing scams.
Important security features of a secure wallet
A wallet is considered highly secure if it is CC EAL5+ certified. This certification is of providing high-security standards that are set for deployments of government-level. Wallets must be portable to provide ease to crypto holders to transfer funds anytime. A secure wallet doesn't need a wired connection with cold storage wallets. Your wallet must use a one-time password generator as it is an additional layer of security that enables users to be aware of all the transactions, and each transaction must take confirmation from the wallet owner. The wallet must never charge fees to transfer the crypto assets other than charging mining fees.